Security Audit Report Template. This rearranges template maintain – every reviews are put away in a single spot, and permits to chop off the retrieve rights to varied templates. Since one security loophole can bring your whole enterprise to its knees, you must strive to get your application and network assessed for vulnerabilities. Along these traces, your prickly examination report template turns into a big instrument in settling upon the exact decisions for your business. Neglect, lack of knowledge in community security, and malicious intent can render a network weak to safety threats.
Here, the fix is determined by the sort of safety vulnerability. Feel free to obtain this template and observe alongside as we go over 5 customization recommendations in your annual evaluations. In most instances it will be the IT manager or administrator in command of the technical workplace operations.
The structure permits reviews to be constant and reduces the effort and time spent in making ready and writing the report. The most crucial characteristic of an ideal VAPT service supplier is its efficiency in providing a comprehensive penetration testing report. Criminals had been in a position to use login credentials, e mail addresses, private assembly URLs, and host keys to affix meetings or use the harvested data for different malicious functions. You might even discover extra from the Microsoft upon the web. Create custom-made lockdown plans for different emergency eventualities.
Supporting these necessities have supplied finish customers with the ability to remotely access corporate information, use of transportable gadgets, and access to cloud companies. Unfortunately, these modifications have also launched additional safety risks that many organizations have didn’t properly account for. Failing to observe changes in network assets, security insurance policies and controls, and user account privileges will lead to an increase threat of critical systems and data being compromised.
However, it’s attainable that somebody may arrange entry points not on that band. If you scan solely the two.four GHz band you can miss access factors which have been put in on a 5 GHz band.
Lack Of A Breach Response Plan
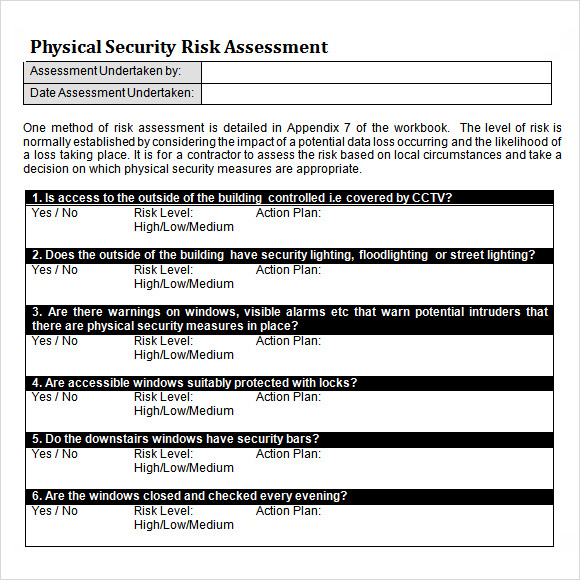
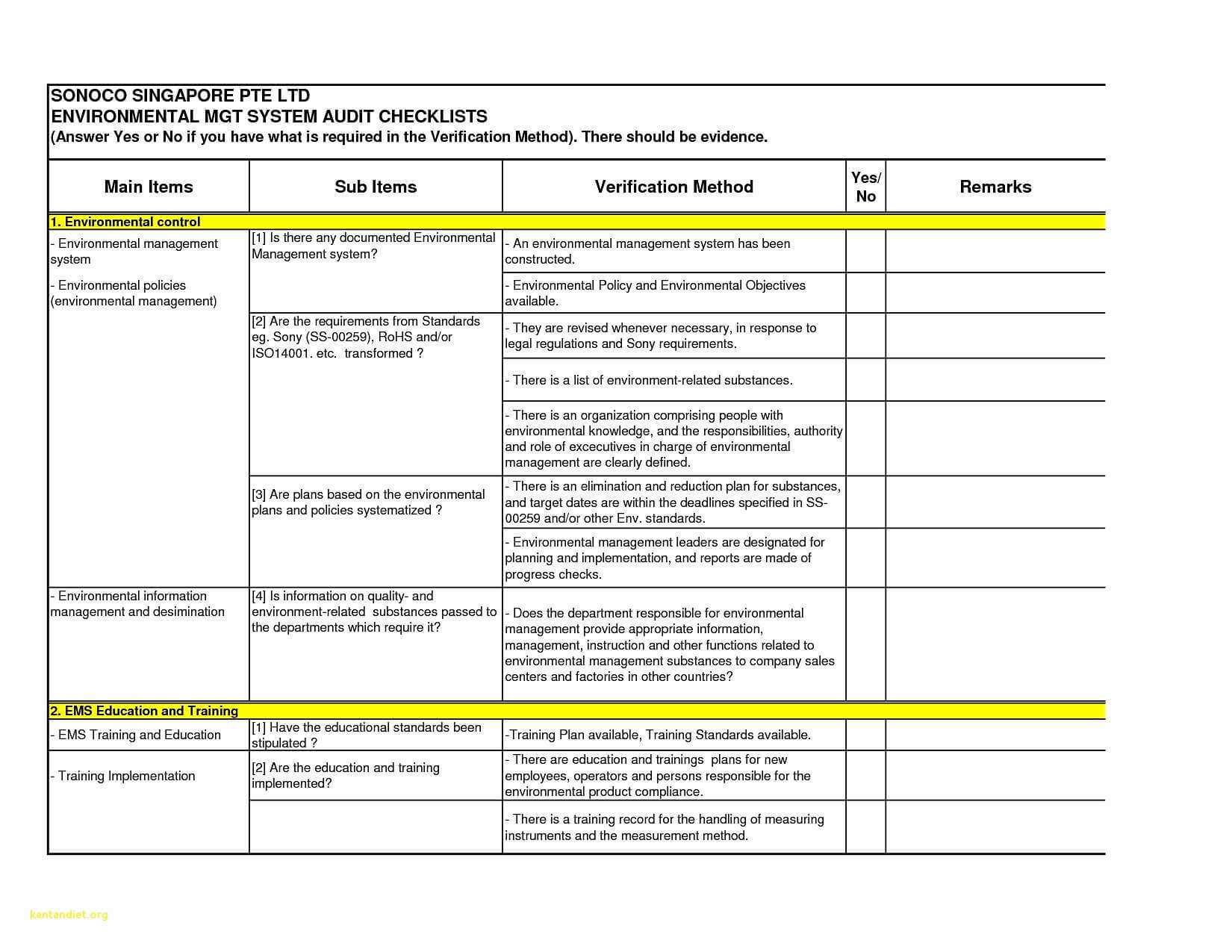
Check out our CyberSecurity Standard templates, together with insurance policies, controls, processes, checklists, procedures and different paperwork. Preparation of a workplace security checklist is a detailed oriented evaluation of your office security system coping with personal, bodily, procedural and data safety. It may be carried out in a quantity of methods, from a full-scale technical evaluation, to easy one-to-one interviews and surveys of the folks in the office and their data of the safety policies already in place.
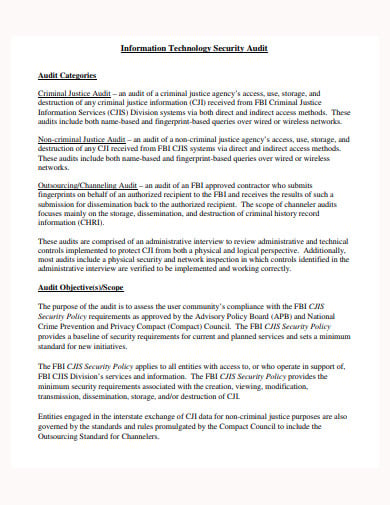
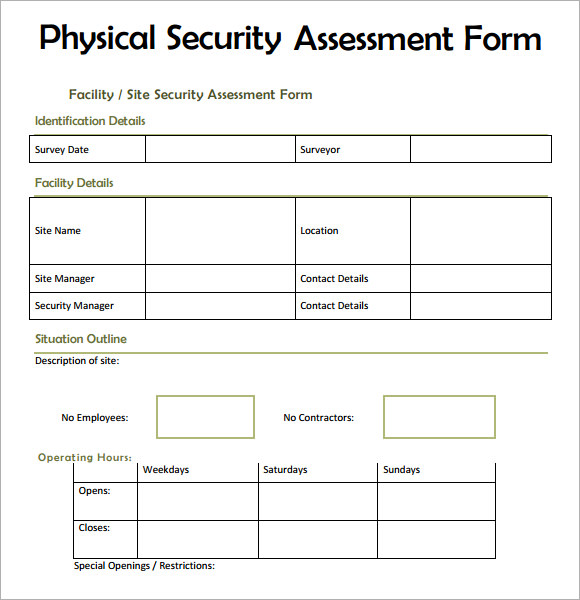
It helps to shortly find any detailed data, such as the auditor’s name, the scope of the audit, the date of the audit, and the variety of pages within the audit report. A security audit could also be performed by a 3rd get together or by the enterprise itself and it doesn’t necessarily need to be a one-time exercise. A enterprise can go for a security audit on a periodic basis.
Security Exams Report
The Payroll Report Template Excel works as a template that helps you prepare your monetary reviews rapidly and easily. This template helps you prepare your month-to-month, quarterly, six-month and year-roun… Social security numbers or medical information ought to be stored in a special location with differing levels of entry to different much less personal information.
They provide a quick and convenient approach to view crucial data in the report. SOC 2 is an auditing process that ensures your service suppliers securely handle your knowledge to guard the interests of your organization and the privateness of its clients.
A few functions require the placing away of Job Progress Report Template in a database. This rearranges template preserve – every stories are put away in a single spot, and permits to separate the open rights to numerous templates. I famous just a single nonattendance of this method – damage intricacy of the code within the…
The finest method to improvise is to maintain on comparing with the previous evaluation and implement new modifications as you encounter success and failure. You now have the required guidelines to plan, initiate and execute a complete inner audit of your IT security. Keep in thoughts that this guidelines is aimed toward offering you with a fundamental toolkit and a sense of direction as you embark on the interior audit process.
Similarly, the following section delves into the workflow and particular actions concerned in web app safety testing. The vulnerability is moderately significant, which means that exploiting it may require meeting certain situations that are not extremely tough to realize.
Despite my grandiose beliefs that I knew everything I wanted to know about all things digital, I hadn’t the faintest idea about the means to spot a fraudulent message from a reliable one. And this type of threat is considered one of the biggest dangers businesses face today.
It Security Audit Report Template
Evidence evaluation can substantiate claims from both get together. The investigator ought to collect physical evidence such as footage, e mail information, paperwork or papers, bodily objects, and so on. and doc investigative interviews. These ought to then be analyzed to determine the relevant details, assess the credibility of disputed facts, and dismiss irrelevant information.
If there are specific conditions that must be met so as to exploit the vulnerability, they should be described. Then comes the description of the bug’s technical details, during which we show how to exploit the bug. At the end of this part of the safety audit report, we should embrace the recommendations that’ll eliminate the risk once launched.
Keeping this in thoughts you have to present an govt summary of the pentesting report for the decision-makers. The govt summary doesn’t cowl technical particulars or terminology however the overview of the main findings is defined in layman’s phrases. The government summary must be quick, crisp, and well-formatted.
- It data the weaknesses, the threat they pose, and attainable remedial steps.
- For instance, a network can consist of hundreds or even thousands of computer systems.
- Customize iAuditor community security audit templates to fit the wants of your group.
- It is important to try to use updated know-how to safe your networks, in any other case, you allow them vulnerable.
- At Astra Security, we now have helped lots of of companies identify and fix their vulnerabilities with our VAPT service.
- Conducting community safety audits might help proactively reinforce cybersecurity and avoid expensive IT incidents.
The account that can be accessed on this means is referred to as a god mode account by the appliance. In the summary, the readers may familiarize themselves with the adopted vulnerability classification. Therefore, we should record all the degrees and add a detailed description to every of them.
Assess the effectiveness of your firewall by reviewing the rules and permissions you currently have set. Assess the scope and depth of the training processes and make sure they’re obligatory for all staff.
Use a security administration system template to make sure you’re adhering to OSHA’s 1970 Health and Safety Act. In this text, you possibly can find out about some great benefits of conducting an ISO audit and the way to construction your personal guidelines so you can pass an ISO audit without a hiccup. Security ratings present a comprehensive, outside-in view of a company’s general cybersecurity posture.
A Penetration Testing report is a doc that incorporates an in depth analysis of the vulnerabilities uncovered in the course of the safety test. It data the weaknesses, the threat they pose, and attainable remedial steps. The Pentest Report offers you a complete overview of vulnerabilities with a POC and remediation to fix those vulnerabilities on priority.
Especially after-hours when there’s no one on the building, or during minimal staffing shifts, video surveillance methods and alert techniques may help stop a safety breach. For example, set a foyer door to remain open during enterprise hours when there’s a front desk particular person on obligation, and set it to mechanically lock and require users to credential in after-hours.
A few purposes require the putting away of Office Incident Report Template in a database. This rearranges template preserve – all reports are put away in a single spot, and permits to separate the retrieve rights to numerous templates.
The breach also brought on the brand to endure a adverse backlash concerning its public picture. This is usually because the security issue is not with the tools per se, however with the way people use these security tools, procedures, and protocols.
A net server ecosystem is intrinsically complicated with extremely connected, heterogeneous services and components working collectively. Reviewing and managing the configuration of the server is, as a result, a really crucial facet for sustaining robust security across multiple layers of an utility. The administrator authorization application uses a cookie that could be obtained by an attacker.
To additional defend data and other confidential information, modify access ranges according to the type corresponding to worker, third-party supplier, or customer. Being involved with cybersecurity for over six years now, his vision is to make cyber security a 5-minute affair.
The Payment Card Industry Security Standards Council developed the PCI DSS to protect against bank card fraud. The auditing process is important for maintaining compliance with IT security standards. Still, the sheer volume of requirements out there is sufficient to make even essentially the most seasoned audit professionals lose sleep at night time.
You can either download the report within the format of PDF or Email. Each vulnerability has a bit throughout the report that describes it intimately and speaks of fixing such flaws and offers an outline of each mitigation with steps to repair .
Each vulnerability ought to include a short title describing the risk. The title must also embrace the criticality level of the vulnerability. Then, we create an outline by which we present the detected threat intimately.
Security Audit Report Template will begin within the manner of the nitty-gritty including the dealing out name, place and site handle. Coming occurring next are the numerous areas you want to search for gone getting an honest targeted examination Security Audit Report Template. From this information, you ought to amass a mental considered the place your rival is at just as your personal business.
In this text, the Application Security Audit Checklist Template will cowl. In today’s technology landscape, organizations are supported by net purposes that act as essential enablers to streamlining operations. While these applications allow automation, wider collaboration, and ease of sharing knowledge.
Make relevant notes for particular audit guidelines items and have visibility of paperless community security reviews from any web site. CyberSecurity Standards What are essential CyberSecurity Standards?
PDFfiller.
Indeed, there are many methods to carry out IT safety danger assessments, and the outcomes might differ widely relying on the method used. It must also be famous that per-forming a risk assessment is a very small a part of the overall threat management course of. Therefore, a safety evaluation and corresponding threat mitigation plan shall be included as a part of the OCFO Conference and Training Approval Package for all USDA Sponsored Conferences and Training Events over $75,000.
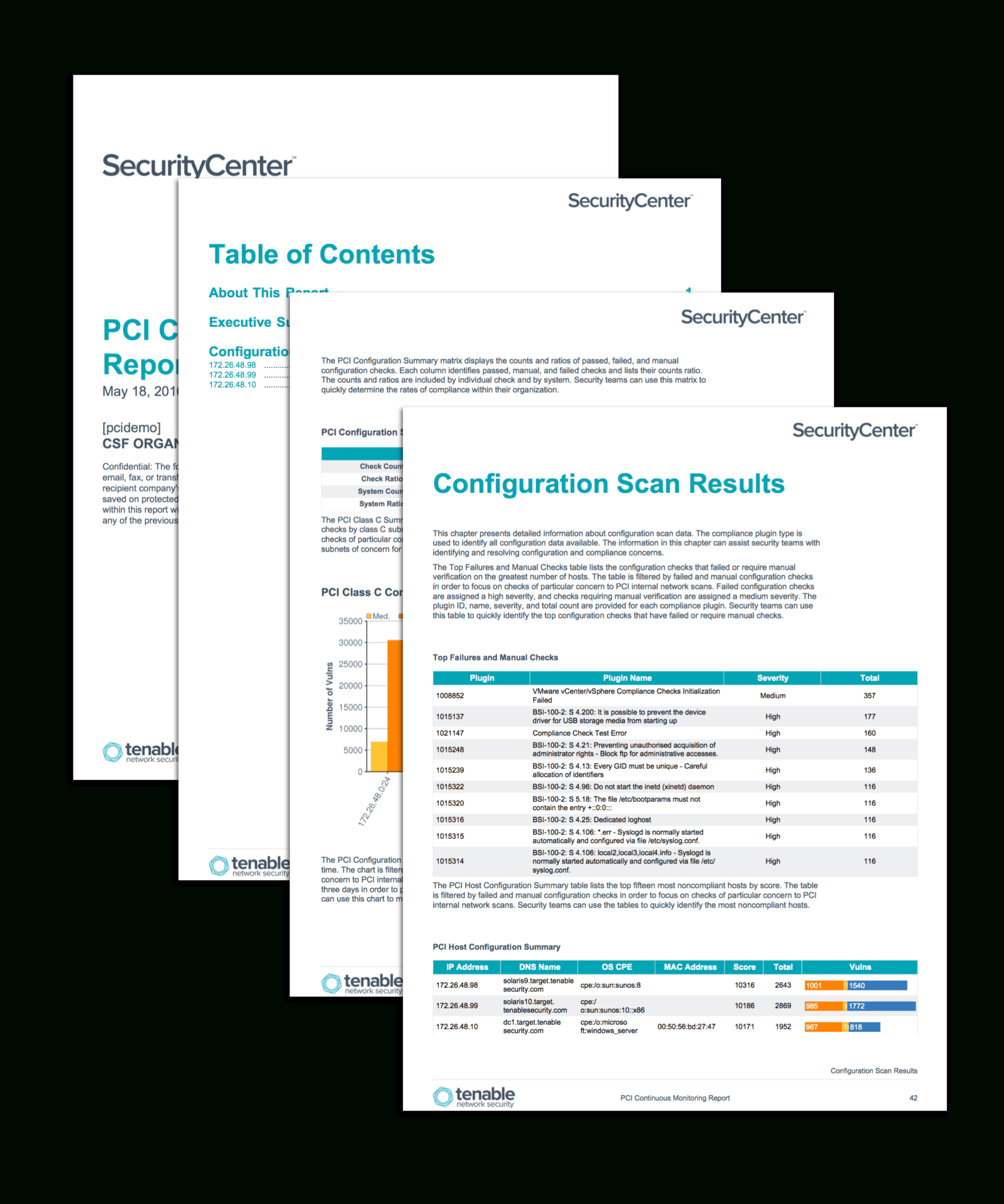
Passive listening collects information to repeatedly detect units and monitor network connections and exercise. Host information and information from different security investments is collected and analyzed to observe activity, identify new property, and detect anomalies and malicious habits. Tenable.sc CV offers a corporation with probably the most complete view of the community, and the intelligence needed to safeguard important assets and delicate information.