Character Report Card Template. It is simpler to move a shell variable intoawk through the use of the -v choice and an awkvariable. We present some minimal explanations, but see a good shell programming e-book when you want to understand things in additional depth. The capacity to make use of octal and hexadecimal constants in awkprogram source code . It can appear in input knowledge by having two successive occurrences of the field separator appear next to each other.
In the discharge after that this extension might be faraway from the distribution. Fcount tracks what quantity of traces within the current file matched the pattern. Character Writer is the subsequent technology of writing software, combining the ability of the Enneagram personality-typing system and the most recent expertise.
Gawk pays consideration to a variety of setting variables.AWKPATH, AWKLIBPATH, and POSIXLY_CORRECT are crucial ones. This is a limitation, and it additionally signifies that you cannot use this to multiplex enter from two or more sources. In addition, gawk offers built-in features for sorting arrays; see Sorting Array Values and Indices with gawk. The argument count controls what quantity of occasions to repeat the action, as in step. • Accessing The SourceAccessing the Git repository.• Adding CodeAdding code to the primary body of gawk.• New PortsPorting gawk to a new operating system.• Derived FilesWhy derived recordsdata are saved within the Git repository.
The following program, extract.awk, reads via a Texinfo source file and does two things, primarily based on the particular comments. Upon seeing ‘@c system …’, it runs a command, by extracting the command text from the management line and passing it on to the system() function (see section Input/Output Functions). Upon seeing ‘@c file filename’, each subsequent line is shipped to the file filename, until ‘@c endfile’ is encountered.
Its objective is to show you tips on how to solve your problems by yourself. When gawk behaves differently from other awkimplementations in particular circumstances, and that habits can’t be attributed to an additional characteristic in gawk. When gawk behaves differently from what’s described on this Web page.
See part Defining Fields by Content for extra info. FIELDWIDTHS #A space-separated record of columns that tells gawkhow to split enter with fixed columnar boundaries.
The abstraction provided by getopt() could be very useful and is type of useful in awk packages as properly. Following is an awkversion of getopt() that accepts both brief and lengthy options. Library features often have to have international variables that they can use to preserve state info between calls to the function—for example,getopt()’s variable _opti(see section Processing Command-Line Options).
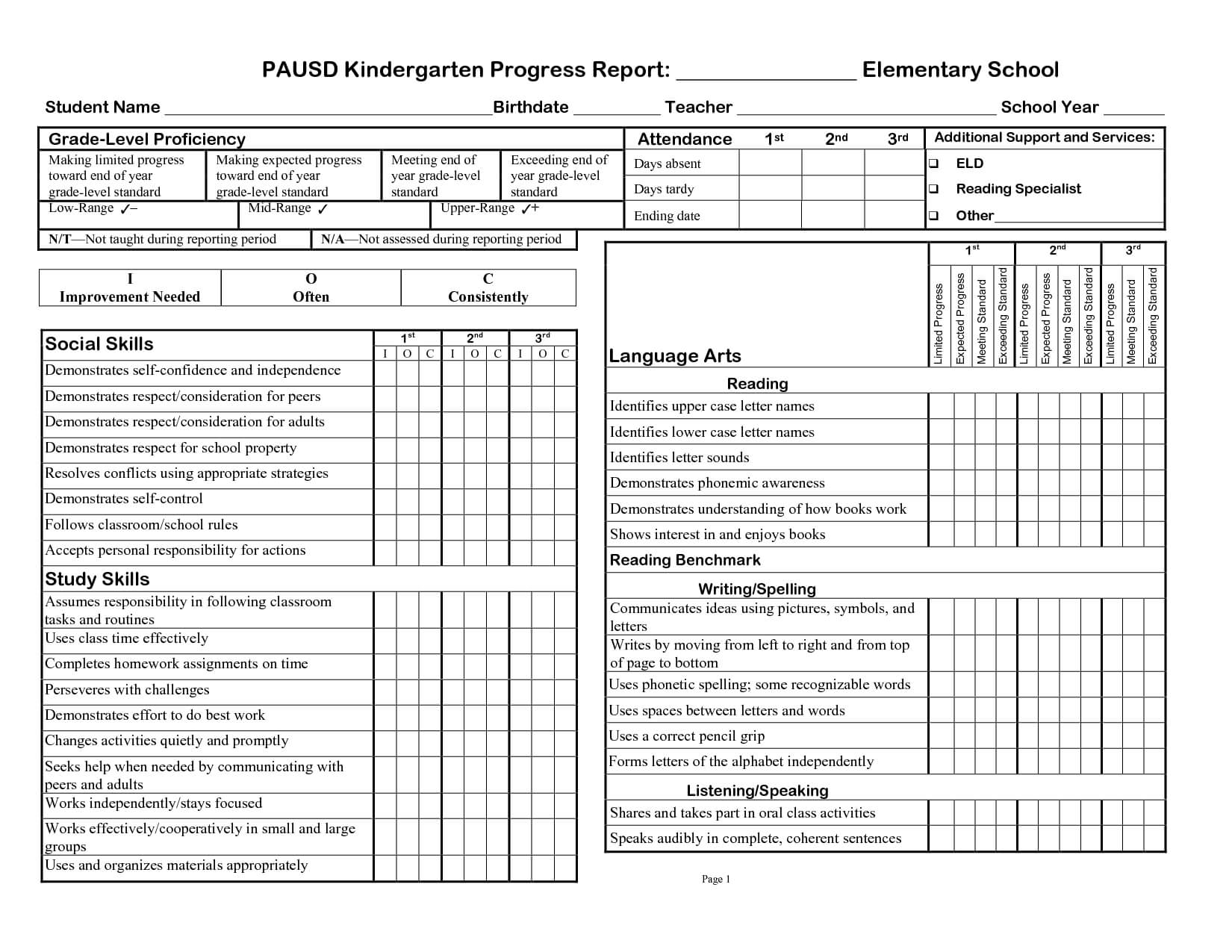
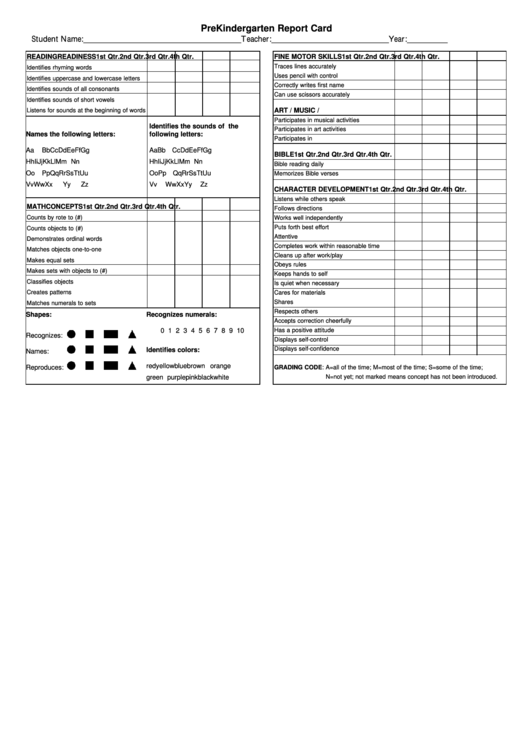
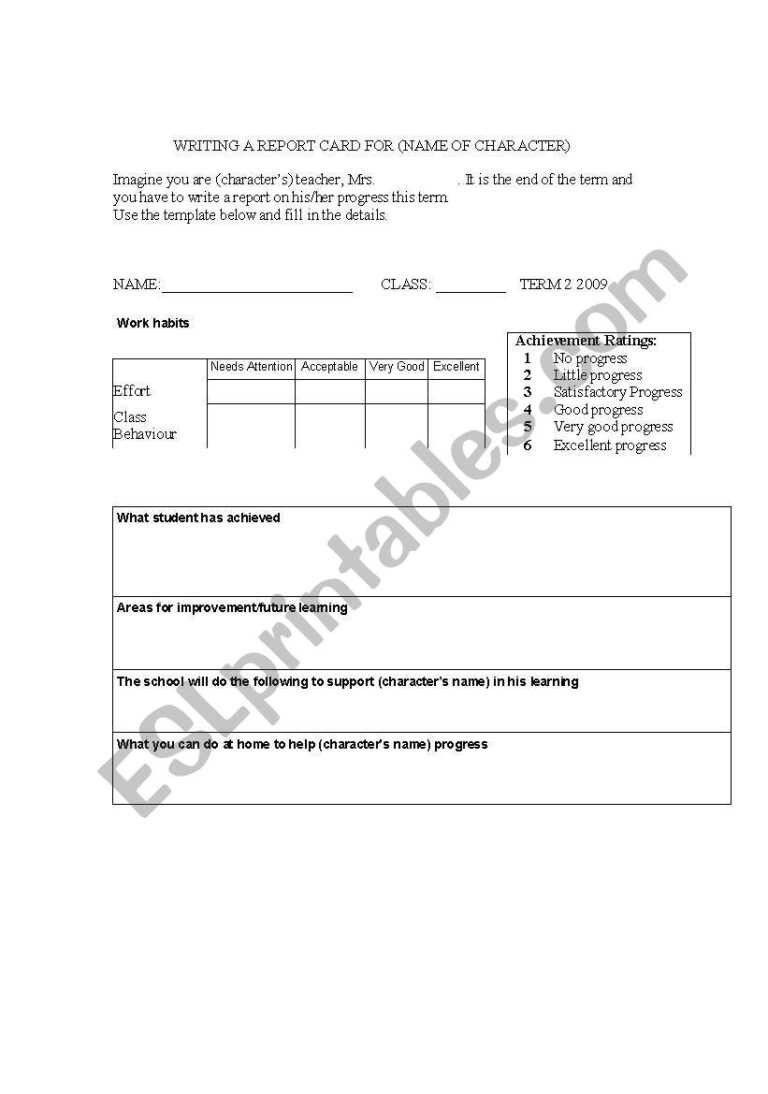
Report Card Comments About Writing, Studying, Math And Generals
RSTARTThe start index in characters of the substring that’s matched by thematch() perform (see section String-Manipulation Functions).RSTART is about by invoking the match() operate. Its value is the place of the string where the matched substring begins, or zero if no match was discovered.
For the file inventory-shipped, $6represents the total variety of parcels shipped for a selected month. The empty string “” has a special meaning as the value of RS. It implies that data are separated by one or more blank traces and nothing else.
Part Ii:Drawback Fixing With Awk
Regular expressions match the leftmost longest textual content within the string being matched. This matters for cases where you have to know the extent of the match, such as for textual content substitution and when the document separator is a regexp. Regexp constants may be used standalone in patterns and in conditional expressions, or as part of matching expressions utilizing the ‘~’ and ‘!
A numeric value less than zero is handled as zero, and a numeric value larger than three is treated as three. Alternatively, string values of “r” or “w” specify that input files and output information, respectively, should use binary I/O.
The tools that extract messages from source code pull out all strings enclosed in calls to gettext(). Each language’s .po file is transformed right into a binary message object (.gmo) file. A message object file incorporates the original messages and their translations in a binary format that permits quick lookup of translations at runtime.
It is represented explicitly inawk applications by inserting two double quote characters subsequent to one another (“”). It can seem in input knowledge by having two successive occurrences of the sector separator seem subsequent to one another.
Browse The Library
However, drafts helpful for the producers adopted at a later stage in the interval. A complete description of the work on this period is given in.
The Global Service for Mobile communications , with the greatest worldwide number of users, succumbs to a number of safety vulnerabilities. In the GSM, solely the airway visitors between the Mobile Station and the Base Transceiver Station is optionally encrypted with a weak and broken stream cipher (A5/1 or A5/2).
Search the goal string target for matches of the common expression regexp. If how is a string starting with ‘g’ or ‘G’ (short for “global”), then substitute all matches of regexp with substitute. Otherwise, treat howas a number indicating which match of regexp to exchange.
It prints every word that is greater than 10 characters lengthy and likewise prints the number of such words. See part String-Manipulation Functionsfor extra information on the built-in function length(). When no data files are listed on the command line, awk reads from the usual input andFILENAME is about to “-“.
For example, you can use the formfeed character (written ‘\f’ in awk, as in C) to separate them, making each record a web page of the file. Any different character might equally nicely be used, so long as it won’t be a part of the data in a report. Thus, common expression matching as carried out when splitting fields with FS isn’t allowed to match the null string; it must at all times match no much less than one character, in order to have the power to proceed by way of the complete document.
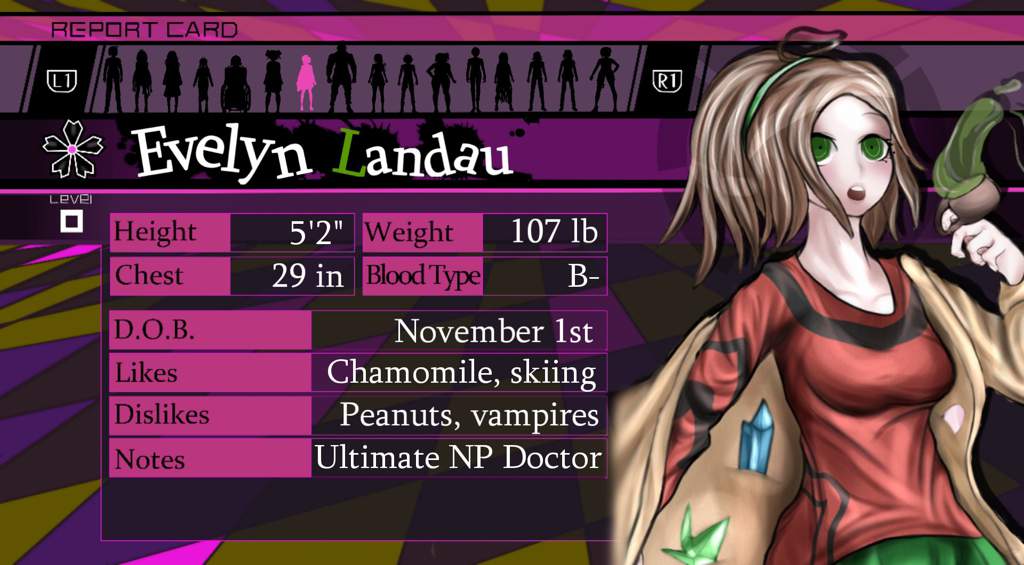
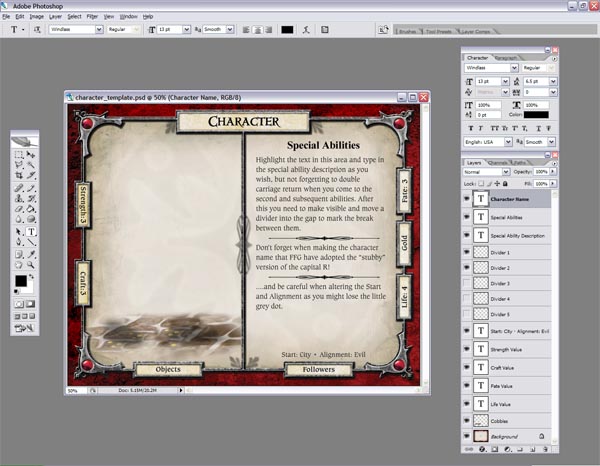
Because I am compulsive like that, I decided to make a personality template sheet with as much details as I can fit in it as humanly potential. How to Make a Homeschool Report Card with Free Printable – This insightful post helps give ideas on what to incorporate in your homeschool report card, additionally a cheat sheet tips on how to grade by quantity or analysis.
This restructured the police into State, Security, and Local Government ranges. The Law on Police reiterated moral necessities, where cops were prohibited from performing or supporting acts referring to “torture or different cruel, inhuman or demeaning treatment or punishment”. This hostility in the direction of Russians remained within the following years, and despite lack of official statistics, police brutality continued to be a problem after Latvia’s independence.
Reset all configurations to default, that’s, the default card fashion to default, clear all custom playing cards, and default to 6 reserved card slots. To reset a configuration merchandise, right-click the configuration merchandise and press Reset.
Some of the built-in capabilities have one or more optionally available arguments. If these arguments aren’t equipped, the capabilities use an affordable default value.
Dynamic extensions need to be compiled with the identical compiler options for floating-point, pointer size, and symbol name dealing with as have been used to compile gawk itself. The pointer measurement is 32 bits, and the image name dealing with must be actual case with CRC shortening for symbols longer than 32 bits.
Their main function was to deliver particular providers of the network operator to any cellphone. The GSM business has identified a selection of potential fraud attacks on cellular operators that may be delivered through abuse of SMS messaging providers. The most severe threat is SMS Spoofing, which happens when a fraudster manipulates tackle data to have the ability to impersonate a consumer that has roamed onto a international network and is submitting messages to the home community.
The awk implementation of cut makes use of the getopt() library function (see section Processing Command-Line Options) and the join() library function . We now examine to see if this option takes an argument and, if so, we setOptarg to the value of that argument .
On methods where the listing entry contains the file kind, the document has a third subject , which is a single letter indicating the sort of the file. The letters and their corresponding file sorts are shown in Table 17.four. “stat”This factor is itself an array, containing the same info as provided by the stat() perform described earlier for itsstatdata argument.
Python permits “Universal Newline Support” when opening a file for studying, when importing modules, and when executing a file. Prepare for the KS2 SATs with these SATs Skills workbooks, flashcards and test papers.
This command format instructs the shell, or command interpreter, to start awk and use this system to process information within the enter file. There are single quotes round program so the shell won’t interpret any awk characters as special shell characters.
You are allowed to use the identical array for each the supply and destarguments, but doing so only is sensible if you’re also supplying the third argument. The features in this section look at or change the text of one or more strings. Return the positive sq. root of x.gawk prints a warning message if x is adverse.
An FBI murder report from 2012 noticed that while black folks symbolize 13% of the US population, they amounted to 31% of those killed by police, and have been responsible for 48% of police murdered. It was discovered by way of Kaiser Family Foundation analysis that simply about half of Black Americans believe they have been victimized by regulation enforcement.
See section Splitting a Large File into Pieces and see part Duplicating Output into Multiple Filesfor examples of each method of removing elements from ARGV. The isarray() perform may be used to check if a component in SYMTAB is an array.
Dcgettext(string [, domain ])Return the translation of string in text domain domain for locale class category. The default value for area is the current worth of TEXTDOMAIN. _”your message here”String constants marked with a number one underscore are candidates for translation at runtime.
Besides the built-in functions, awk has provisions for writing new capabilities that the relaxation of a program can use. The second half of this chapter describes theseuser-defined functions.
The num_actual_args argument tells the C perform how many actual parameters were passed from the calling awk code. The reminiscence allotted by these features must be freed withgawk_free().